The world of the darknet is often shrouded in mystery, filled with various platforms that facilitate a range of activities. Among these platforms, the abacus darknet url has gained attention for its unique offerings. Understanding how this aspect of the darknet operates is crucial for anyone seeking to explore or become informed about its implications. This article will delve into the characteristics, functionalities, and potential risks associated with the abacus darknet url while providing insights into the broader landscape of darknet environments.
Abacus Darknet Url
If you’re looking to validate your security posture, identify hidden risks on the dark web, or build a more resilient defense strategy, DeepStrike is here to help. Who is likely to exit scam next? This way if a market vanishes, they lose minimal funds.
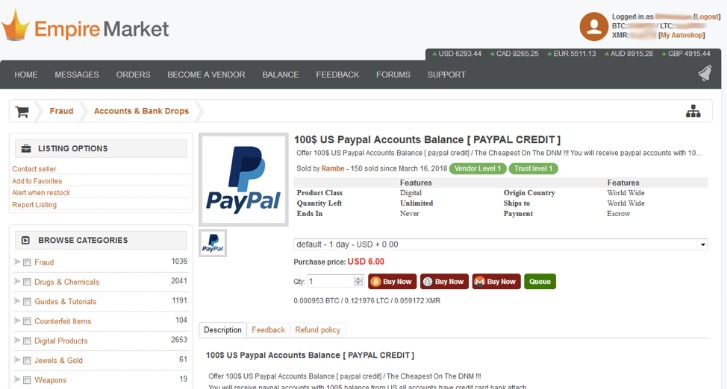
- Threat actors can find malware, ransomware, stolen credentials, hacking tools, and other services for sale.
- Create a username with no ties to your real identity, and never reuse passwords from other sites.
- STYX Market launched in early 2023 and quickly became a hub for financial cybercrime.
- The most reliable and longest-running darknet marketplace since 2021
- In the wake of several takedowns of fraud focused markets like the infamous Genesis Market in April 2023, STYX quickly filled the gap and attracted a lot of attention from cybercriminal circles.
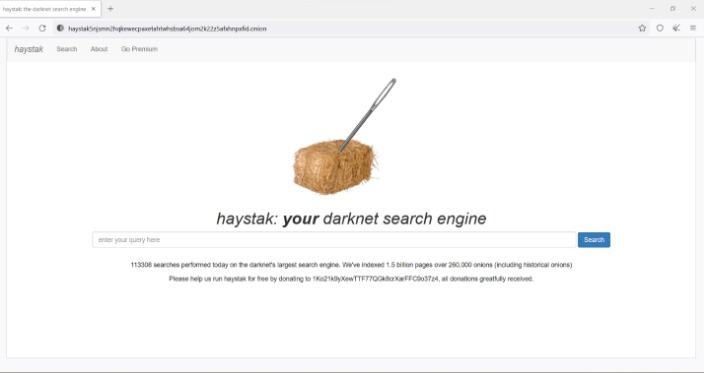
The abacus darknet url is part of a specialized network that is not indexed by standard search engines. It operates using specific privacy protocols, making it a haven for users seeking anonymity. This aspect is essential for various activities, from secure communications to the exchange of information that may not be accessible through conventional browsers.

Understanding the Darknet
To fully grasp what the abacus darknet url represents, it is important to understand the wider context of the darknet. The darknet is a subsection of the internet that requires special software, configurations, or authorization to access. Unlike the surface web, which is the part we regularly use, the darknet hosts sites that are often hidden from traditional search engines. This underground aspect allows users to communicate freely and share information without the typical traces left behind on the surface web.
Threat actors can find malware, ransomware, stolen credentials, hacking tools, and other services for sale. Some vendors offer “access as a service” where they maintain persistent access to compromised networks and sell it repeatedly to different buyers. Transactions are conducted in cryptocurrency, typically Bitcoin or Monero, with funds held in escrow by the marketplace until the buyer confirms receipt. Third, the ransomware economy has created a robust market for corporate data. These specialists compromise corporate networks and then sell that access to ransomware operators, data thieves, or espionage groups. High-profile markets sometimes close overnight, and new markets can surge in popularity quickly.
(II)Tokenization of Real-World Assets refers to the use of encryption technology and distributed ledger or similar technologies to transform ownership rights, income rights, etc., of assets into tokens (tokens) or other interests or bond certificates with token (token) characteristics, and carry out issuance and trading activities. Without the consent of relevant authorities in accordance with the law and regulations, any domestic or foreign entity or individual is not allowed to issue a RMB-pegged stablecoin overseas. They do not have legal tender status, should not and cannot be circulated and used as currency in the market. Stick to well-vetted platforms, use privacy coins like Monero for anonymity, and withdraw funds regularly instead of leaving large balances. History shows that peers who pulled similar stunts—like the voluntary shutdowns of ASAP and Agora Markets, or the infamous Evolution exit scam—slipped away unscathed, living to spend another day. And with Incognito Market seized by authorities in March 2024, Abacus’s grip tightened to over 70% of the Bitcoin-backed Western darknet scene.
How the Abacus Functions
The abacus darknet url facilitates various functions, such as secure transactions and private communications. Users engage with this platform for diverse reasons, including the search for privacy and the need to operate outside of governmental oversight. This highlights a significant aspect of darknet usage: the balance between freedom and risk. While many use these platforms for legitimate reasons, others may exploit them for illegal activities.
Risks Associated with the Darknet
Engaging with the abacus darknet url or any darknet platform carries inherent risks. The anonymity that attracts many users can also lead to dangerous encounters, scams, and the potential exposure of personal information. Additionally, there’s the risk of encountering illicit content or being involved in illegal activities that can have severe consequences. For this reason, it’s vital for users to proceed with caution and ensure they prioritize their safety and security online.
Staying Informed
Being informed about the workings of platforms such as the abacus darknet url can empower individuals. Understanding the motivation behind darknet usage and its implications is essential for anyone considering exploring this hidden part of the internet. Education about online safety, privacy rights, and the technology involved can help users navigate these environments more responsibly.
Conclusion
The abacus darknet url serves as an example of the complexities involved in the darknet ecosystem. While it offers tools for privacy and security, it also requires users to navigate a landscape filled with pitfalls. By remaining well-informed, individuals can better mitigate risks and utilize the internet in a way that aligns with their values and needs. As the digital landscape continues to evolve, staying updated on these topics will be crucial for maintaining personal safety online.