In recent years, the landscape of the internet has transformed significantly, unveiling hidden realms beyond the conventional web. One such realm is the darknet, a part of the internet that requires specific software and configurations to access. Among various activities conducted in this clandestine environment, the existence of darknet markets has gained attention. While often associated with illegal goods and services, understanding the dynamics of these markets can provide valuable insights into digital privacy, security, and the ongoing evolution of online commerce.
Accessing Darknet Market
Cybersecurity professionals also monitor the dark web as an important source of threat intelligence. Cybercriminals take advantage of this anonymity to cloak their illegal activities. Both the people visiting dark websites and the people hosting them cannot be easily identified. Dark web networks use methods such as multilayered encryption and indirect routing to hide users’ identities. The dark web is home to web pages, messaging channels, file-sharing networks and other services similar to the regular, or “open,” web. Vortex is an anonymous, responsive, and user-friendly darknet marketplace with an excellent user experience.
- In 2002, the dark web grew significantly when researchers supported by the US Naval Research Laboratory built and released the Tor network.
- Users can also betray their own identities by misconfiguring or improperly using a dark web browser or network.
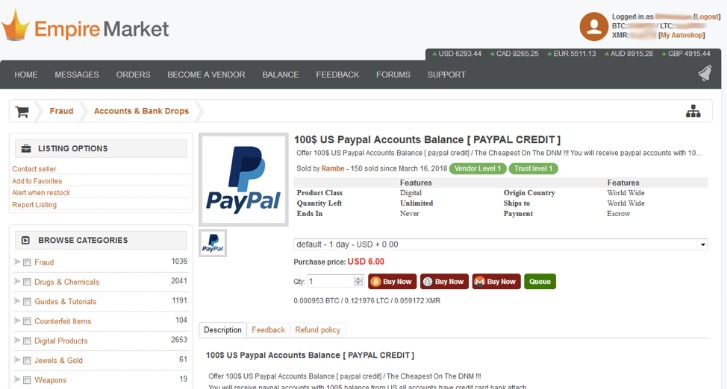
- A large number of services pretend to be a legitimate vendor shop, or marketplace of some kind in order to defraud people.
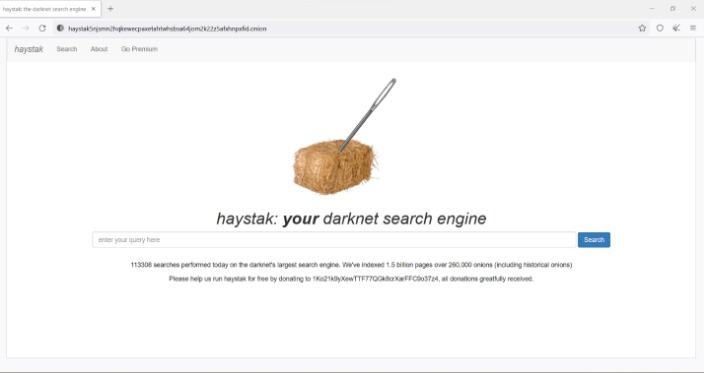
- To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis.
While some users may attempt in-person trades or use peer-to-peer fiat services off-platform, crypto is the only practical currency for darknet markets at scale. Commercial darknet markets mediate transactions for illegal goods and typically use Bitcoin as payment. Tor browser and Tor-accessible sites are widely used among the darknet users and can be identified by the domain ".onion". The dark web, also known as darknet websites, are accessible only through networks such as Tor ("The Onion Routing" project) that are created specifically for the dark web. Special markets also operate within the dark web called “darknet markets”, which mainly sell illegal products like drugs and firearms, paid for in the cryptocurrency Bitcoin. The RAND Corporation reports that researchers at Carnegie Mellon University concluded that darknet markets accounted for $100 million to $180 million in total sales volume in 2015.
Accessing the darknet market involves several key steps and precautions. Below is a guide aimed at educating users about the process and associated risks:
Tools Needed to Access Darknet Markets
- Tor Browser: This is the primary tool for accessing the darknet. It anonymizes the user's identity by routing internet traffic through multiple servers.
- VPN Service: Using a Virtual Private Network (VPN) adds an extra layer of security and private browsing.
- Secure Operating System: Consider using an OS designed for privacy, such as Tails, which runs from a USB stick or DVD without leaving a trace on the computer.
Steps to Access Darknet Markets
- Estimates vary, but it's safe to say the surface web comprises about 10% of the total internet.
- Regardless of which dark web search engine you use, it’s extremely important to exercise caution when using a dark web search engine.
- Businesses should prepare for more sophisticated ransomware campaigns, potentially leveraging AI to exploit security gaps.
- Escrow is the most basic transaction model, that is, the market acts as a somewhat trusted “third party” between buyers and vendors.
- The “deep web” includes everything on the internet that is password-protected, paywalled, or even just protected from crawling by a site’s robots.txt file.
- When you search for your favorite recipe, check the news or browse social media, you’re using the surface web.
- Download and Install Tor Browser: From the official Tor Project website, ensuring you are downloading the genuine software.
- Connect to a VPN: Activate your VPN service before launching the Tor Browser for added security.
- Access the Darknet: Open the Tor Browser and enter an .onion URL to reach a darknet market. These URLs aren't found on the standard web; they are often shared on forums or private networks.
- Create a Pseudonymous Identity: Setting up a username and email that do not reveal your real identity is crucial when interacting on these platforms.
- Use Cryptocurrency for Transactions: Most darknet markets operate using cryptocurrencies like Bitcoin to maintain transactional anonymity.
Risks Associated with Darknet Markets
Accessing the darknet market comes with inherent risks. Some of these include:
- Legal Consequences: Engaging in illegal activities on the darknet can lead to severe legal repercussions.
- Scams and Fraud: Darknet markets are notorious for scams. Users must be cautious and do proper research before engaging in transactions.
- Malware Threats: The risk of encountering malicious software is higher in the darknet, potentially compromising personal devices.
Frequently Asked Questions (FAQs)
Q: Is accessing the darknet legal?
A: Accessing the darknet itself is legal in many jurisdictions; however, participating in illegal activities is against the law.
Q: Can I be tracked while using the darknet?
A: While the Tor network provides anonymity, users should always take additional precautions, like using a VPN, to minimize tracking risks.
Q: What types of goods and services are found on darknet markets?
A: Darknet markets feature a wide range of items, from legal products to illegal drugs, counterfeit documents, and hacking services. Caution is always advised when exploring these markets.
Understanding how to access the darknet market can help educate users about online privacy and the importance of safe internet practices. Awareness of the risks and legal implications is crucial for anyone considering delving into this hidden part of the internet.