The adress darknet refers to a part of the internet that is not indexed by traditional search engines and requires specific software to access. Understanding how it operates is essential for safety and awareness in a digitized world. This article will delve into the unique characteristics of the darknet, its uses, and the precautions individuals should take if they choose to explore this hidden part of the internet.
What is the Darknet?
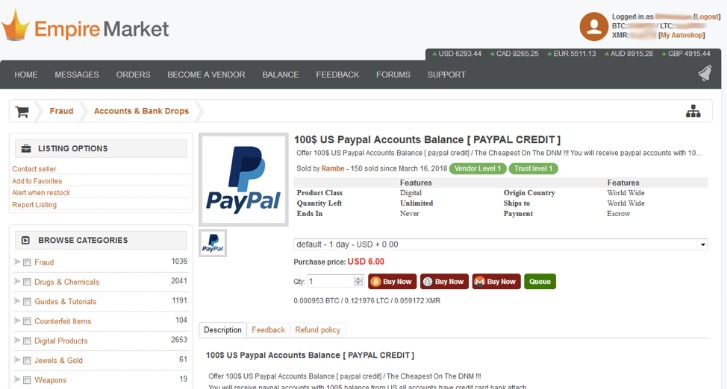
The current leak of one million credit cards by the threat actor appears to be another marketing move to attract potential clients from hacking and cybercrime forums and increase the platform’s popularity. At the time of this publication, the marketplace holds an inventory of over 2,749,336 credit cards, with an average price per card of $US 6. In early August 2021, a threat actor known as AW_cards published a data leak containing details of approximately one million stolen credit cards on several Dark Web hacking forums. Black Ops Market is the future of darknet markets. Vortex is an anonymous, responsive, and user-friendly darknet marketplace with an excellent user experience.
The darknet forms a small sector of the deep web, comprising encrypted networks that ensure anonymity for users. It operates using software like Tor (The Onion Router) or I2P (Invisible Internet Project), which anonymize user activity and website usage. This secure structure makes the darknet both a refuge for privacy advocates and a marketplace for illicit activities.
The Silk Road was an online black market where users could buy and sell illicit goods anonymously. Launched in 2011 and shut down by the FBI in 2013, Silk Road paved the way for today’s underground world of dark web marketplaces. A virtual private network (VPN) masks your IP address and encrypts your online activity, making it nearly impossible for cybercriminals—or anyone else—to uncover your real IP.
- For example, Facebook’s facebookcore listens on both HTTP (port 80) and HTTPS (port 443).
- A further Base64-encoded JavaScript file is downloaded as addon.js.
- Default.js is Base64 encoded JavaScript that functions as a command loop, periodically sending logs to the C2, and checking for new payloads to execute.
- Now you’ll find that the HiddenServiceDirectory (i.e., /var/run/tor/test-onion-config or /tmp/test-onion-config) has been created.
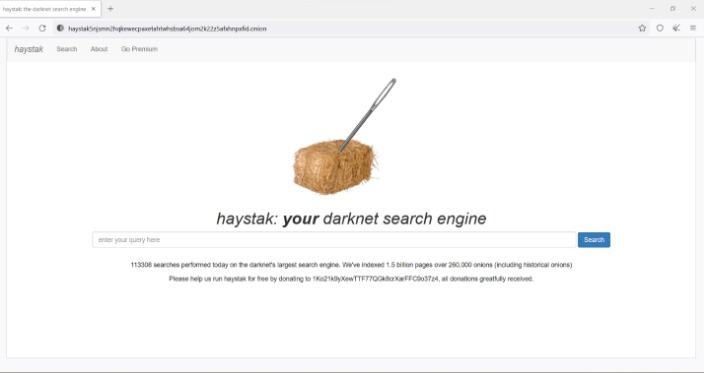
How to Access the Darknet
To adress darknet websites, users typically download and install the Tor browser. This special browser helps protect users' identities by routing their connection through a series of volunteer-operated servers, making tracking difficult. After the installation, users can access .onion domains, which are specific to the Tor network.
Uses of the Darknet
The darknet has its fair share of legitimate and illegitimate uses. On the positive side, it serves as a platform for whistleblowers, journalists, and activists who require security and privacy to express dissenting opinions, especially in countries with oppressive regimes. It also hosts forums for discussions about topics that may be restricted in open forums.
On the other hand, the darknet is often associated with unlawful activities, such as the sale of drugs, weapons, and stolen data. Cybercriminals exploit the anonymity provided by the darknet to conduct nefarious operations, making it a space of caution for potential users.
Risks of Navigating the Darknet
Exploring the darknet comes with significant risks. The anonymity that protects users can also shield malicious actors. Engaging in shady marketplaces or forums can lead to scams, hacking attempts, or exposure to harmful content. Additionally, local laws may prohibit accessing certain materials or sites within the darknet, posing legal risks to users.
Safety Precautions
- They may be compensated as a marketing affiliate of Aura, but their ratings are all their own.
- A leaked email address doesn’t always put you in immediate danger — but it can lead to more serious threats, including hacking and identity theft, if you don’t act on it.
- To work around this, the Extended Instruction Pointer (EIP) register can be manipulated to point to the start of the hook function instead, which will cause it to run instead of the DllMain function.
- By emphasizing anomaly-based detection and response, Darktrace can effectively identify devices affected by ransomware and take action against emerging activity, minimizing disruption and impact on customer networks.
- As a result, macOS threats rNJ1 ely more heavily on social engineering instead of vulnerability exploitation to deliver payloads, a trend Darktrace has observed across the threat landscape .
- “N/A” also denied ever giving admin access to IntelBroker, claiming it was part of a strategy to divert law enforcement’s attention away from the original owners.
For those who choose to adress darknet, it’s crucial to take safety measures:
- Use a reliable VPN: This adds an extra layer of anonymity beyond the Tor browser.
- Avoid sharing personal information: Maintain a strong separation between your real identity and your online persona.
- Be skeptical of offers: The darknet is rife with scams, so exercise extreme caution when making transactions or engaging in discussions.
Conclusion
In summary, the decision to adress darknet carries significant weight. While it offers a space for privacy and free expression, it is also a hub for illegal activities that can put users at risk. Understanding the functioning of the darknet, along with the necessary precautions, can empower individuals to navigate this hidden corner of the internet more safely and responsibly.