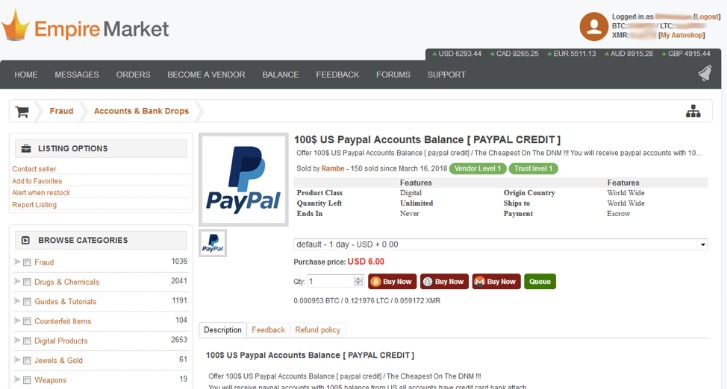
These variations can be attributed to factors like geographic isolation, strict border controls, lenient laws on illegal items, high prices, tight internet control, and the general accessibility of illegal goods. The quality of products is attributed to the competition and transparency of darknet markets which involve user feedback and reputation features. Later markets such as Evolution ban "child pornography, services related to murder/assassination/terrorism, prostitution, Ponzi schemes, and lotteries", but allow the wholesaling of credit card data.
In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace. Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes. One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Share sensitive information only on official, secure websites.
Second, the dark market sites accepted payments for their illicit goods and services in Bitcoin or similar electronic currency designed to be as anonymous as cash. "We will continue to use all of our resources and work closely with our U.S. and international law enforcement partners to shut down these hidden black market sites, and hold criminals accountable who use anonymous Internet software to peddle their illegal activities." This action constitutes the largest law enforcement action to date against criminal websites operating on the Tor network, a special network of computers on the Internet designed to conceal the true IP addresses of the computers on the network.
The digital landscape has evolved significantly over the years, giving rise to various platforms that operate in both the light and dark corners of the internet. One area of increasing interest is the realm of darknet markets. These platforms facilitate the exchange of goods and services, often operating outside the confines of traditional legal frameworks. Understanding how these markets work, along with the active darknet market urls, can help individuals make informed decisions, protecting themselves from potential risks while promoting awareness about the realities of the cyberspace they navigate.
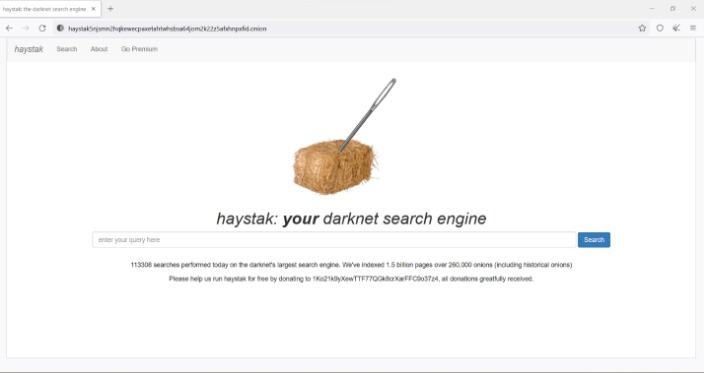
Active Darknet Market Urls
Darknet markets are websites accessed via specific software, allowing users to find goods and services that may not be available through conventional means. These markets are primarily accessed using Tor, a network that anonymizes user activity, making it difficult to trace locations and identities.
What Are Darknet Markets?
Darknet markets serve as e-commerce platforms where vendors can sell a variety of products, including legal goods, illicit substances, and counterfeit items. The anonymity offered by these markets can attract users with different intentions. Many people are curious about these platforms due to the allure of forbidden items, while others may seek out unique products that are hard to find elsewhere.
Types of Goods and Services
On the surface, one may find an array of products ranging from digital art to privacy tools and cryptocurrencies. However, it is vital to recognize that many items sold may involve illegal activities. Awareness of what is available in the realm of active darknet market urls is essential, as it can help users understand the potential legal and personal risks associated with engaging in these markets.
Navigating Active Darknet Markets
When exploring the dark web, navigating these markets requires caution. It’s important to use proper security measures, including VPNs and secure browsers, to maintain anonymity. Users should also be aware of potential scams, subpar products, and other threats. While participating in these markets may appear enticing, it's crucial to weigh the consequences that could arise.
- “Synthient expects to observe a growing interest among threat actors in gaining unrestricted access to proxy networks to infect devices, obtain network access, or access sensitive information,” the report observed.
- Tor, for example, uses multi-layered encryption to create anonymous communication over a computer network.
- If you are wondering how to access onion websites?
- To access Tor, download the Tor Browser from TorProject.org/download/.
- The Reactor graph below shows this vendor’s connection with drug vendors on Abacus Market.
Legal Implications and Risks
The existence of active darknet market urls often comes with significant legal implications. Many transactions can involve illegal goods, and buyers may find themselves entangled in law enforcement investigations. Awareness is key; understanding the legal landscape and the consequences of engaging in such activities is essential for anyone considering navigating these markets.
Conclusion
- The dark web is so dark that it allows you to view content that search engines haven’t even indexed, and it can’t be reached on traditional web browsers.
- After AlphaBay’s shutdown, many users migrated to Hansa, unaware it was under surveillance.
- There’s high exposure to malware and cybersecurity threats that can steal your personal information.
- Many operators have since moved to accepting only Monero (XMR), a privacy coin with features designed to boost anonymity and reduce traceability.
Understanding the realities of darknet markets and their active darknet market urls is important for anyone interested in the digital world. Awareness and education about these markets can empower individuals to protect themselves while navigating online spaces. Whether for curiosity or necessity, remaining informed can help individuals make better decisions in a complex and often risky environment.