The darknet remains a complex and often misunderstood part of the internet that operates beyond the reach of standard search engines. While many associate it with illicit activities, it also serves as a platform for free speech, privacy protection, and encrypted communication. Understanding the active darknet markets is essential for anyone wishing to navigate this hidden part of the web safely and informedly. This guide aims to delve into what these markets are, how they operate, and their implications for users.
Add industry-leading blockchain data to your intelligence suite Cross-chain forensics to surface leads and analyze criminal activity Mission-critical tools and datasets to thwart complex crypto-enabled crime Fully configurable risk rules to surface the activity you care about
Active Darknet Markets
State sponsored groups use the dark web as an extension of their wider operations. For anyone responsible for protecting a business, this shifting space can conceal early warning signs of attacks, leaked credentials, or emerging partnerships between threat actors. Hackers migrate between forums depending on who they trust and which platforms survive law enforcement pressure. For example, whistleblowers might contact journalists on the dark web to protect their identity. You can only reach it through browsers that hide a user’s location and identity, such as onion sites.
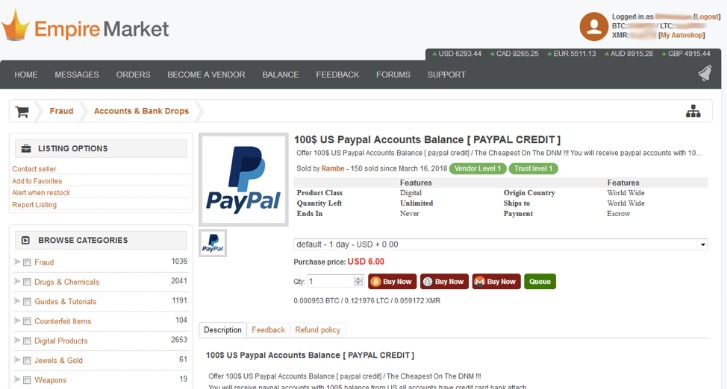
Active darknet markets are online platforms where users can buy and sell various goods and services, often anonymously. These markets primarily operate through the TOR network, utilizing its encryption to provide anonymity for both buyers and sellers. While the majority of items found on these platforms are illegal, ranging from narcotics to counterfeit goods, there’s also a presence of legal offerings like privacy tools and digital services.
Components of Darknet Markets
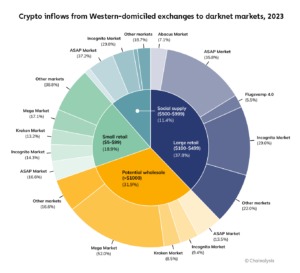
Darknet markets usually encompass several key features: user reviews, escrow services, and dispute resolution. These components are designed to build trust in an otherwise highly anonymous environment. Each transaction is typically facilitated using cryptocurrencies, which adds another layer of anonymity. Popular cryptocurrencies such as Bitcoin or Monero are preferred due to their decentralized nature and relative privacy features.
Exploring the Darknet Ecosystem
- We now turn to the analysis of how migrant users decide where to migrate.
- In this blog, we’ll take a closer look at how these hidden markets operate and the implications they have for cybersecurity and law enforcement.
- We perform the same procedure to compute the daily time series of multibuyers but using the daily time series of buyers obtained from step 2.
- Notably, the number of buyers and sellers significantly drops after the operation Bayonet in the last quarter of 2017, which shut down AlphaBay and Hansa markets, causing a major shock in the ecosystem34.
The activity within the active darknet markets is not static; new platforms emerge while others vanish, often due to law enforcement actions or internal conflicts. Generally, these markets are categorized as either centralized or decentralized. Centralized markets operate under a single entity's control, while decentralized markets rely on a distributed model that can be harder to shut down.
Risks and Precautions
While navigating active darknet markets, users should be acutely aware of the risks involved. The likelihood of encountering scams, law enforcement activities, or harmful actors is relatively high. For this reason, it's crucial to implement safety measures. Using a Virtual Private Network (VPN), practicing good cyber hygiene, and remaining aware of the legal implications of spending time on these platforms are essential actions for safeguarding both personal and digital security.
The Role of Law Enforcement
Law enforcement agencies globally are increasingly focused on monitoring active darknet markets. Projects like Operation DisrupTor have successfully shut down several well-known platforms, highlighting the ongoing battle between illicit vendors and authorities. Understanding this dynamic can aid users in recognizing the temporal nature of these markets and the importance of remaining cautious.
Conclusion
While active darknet markets might intrigue a variety of users, they pose unique challenges and risks. Education is key to navigating these waters, with an emphasis on safety, legal awareness, and the ethical implications of actions taken within this hidden digital landscape. For those who understand the complexities involved, the darknet can provide a unique glimpse into the balance between privacy, freedom, and the nature of illicit trade.